Poor Security at Online Proctoring Company May Have Put Student Data at Risk
Leaked software from Proctortrack raises questions about how carefully schools evaluate test-monitoring companies
Michelle Nguyen, a freshman at Western University in Ontario, didn’t pay much attention when she got an email earlier this year about Proctortrack, the anti-cheating app her college is requiring students to turn on for the kind of remote test-taking that has become widespread during the pandemic.
But as she started using the software, Nguyen felt uneasy. She had to let Proctortrack access her computer’s web camera, record video of her in her bedroom throughout the test, and perform a facial recognition scan. It bothered her, Nguyen says, “but I didn’t have a choice. It was either that or my grades.”
During a recent exam, Nguyen had trouble uploading a document at the end of the exam and broke out in tears. “I don’t like to cry in front of people,” Nguyen says. “Now Proctortrack has a video of me crying. It’s very, very uncomfortable.”
Nguyen isn’t alone. College and high school students across the country have objected to online proctoring programs from Proctortrack and a number of other companies, such as Proctorio, ProctorU, Honorlock, and Respondus Monitor, which all perform surveillance on students while they take tests. The students say the systems are intrusive and make remote exams very stressful.

Proctortrack’s source code ‘was a ticking time bomb.’
Chief technology officer for cybersecurity firm Disconnect
The proctoring companies take varied approaches to judging whether students are cheating. First, they confirm that the person taking a test really is the student. Proctortrack, as an example, says it uses continual facial recognition through an exam, along with knuckle scans that are measured against a biometric profile stored by the company.
During the test, some companies use a real person to watch students, a technique favored by companies including ProctorU. Others, such as Proctorio, prioritize artificial intelligence for analyzing videos. These systems can automatically look for behaviors, eye movements, and other activities that can indicate cheating, according to proctoring companies' claims.
Even before the Proctortrack security problems came to light, some students, privacy advocates, and educators criticized the rapid adoption of such services by schools coping with the pandemic. Reporting in the New York Times, the Washington Post, and elsewhere have documented serious complaints.
In some cases, these reports say, facial recognition features had trouble recognizing dark-skinned students during timed tests. In other cases, students worried about being accused of cheating because of disabilities, such as one student concerned about her chronic tic disorder because lots of facial and eye movements can be flagged as suspicious. Others were worried about being interrupted by a younger sibling, because the sound of voices in the background may be considered a sign of cheating. Students who don’t have their own bedrooms or who lack stable broadband access can also be disadvantaged by the systems. Many students just found it creepy to be recorded at home or watched at close quarters by a stranger whom they couldn't see.
Last week, a group of Democratic U.S. senators wrote to the heads of three leading proctoring services (not including Proctortrack), asking how they are protecting students' civil rights.
Education technology companies often “are given a trust and a responsibility that they haven't proven that they deserve and have earned,” says Akil Bello, the senior director of advocacy and advancement for Fair Test, an education advocacy group. The problem raises serious questions about “the implications for students who are being forced to expose themselves to unethical operators in order to complete their education.”
What Went Wrong at Proctortrack
In late September, what appeared to be Proctortrack’s source code—the underlying programming for its proctoring system—was leaked online, with a link to it posted on a site called RaidForums that is notorious for hosting hacked databases.
Hackers later disabled the company website and sent offensive emails, which they wrote, from official Proctortrack email addresses. The website was reportedly redirected to a music video for Rick Astley’s "Never Gonna Give You Up," in a “rickrolling” prank that was popular a decade ago. CR could not confirm whether the same hackers were responsible for all of these incidents.
The service was taken offline for a week while the breach was investigated.
Then, on Oct. 21, the CEO, Kumar, issued a statement saying that the company had undergone an independent security audit and that any problems had been fixed.
Consumer Reports privacy researcher Bill Fitzgerald was contacted soon after the breach by two freshmen at Ohio’s Miami University. The students, Lucy Satheesan and Erik Johnson, are part of a vocal movement of students across college campuses who are pushing back against the use of proctoring software. The two students say they’ve never used Proctortrack, but after learning of the data breach in a group chat, they downloaded a copy of the source code that was posted online.
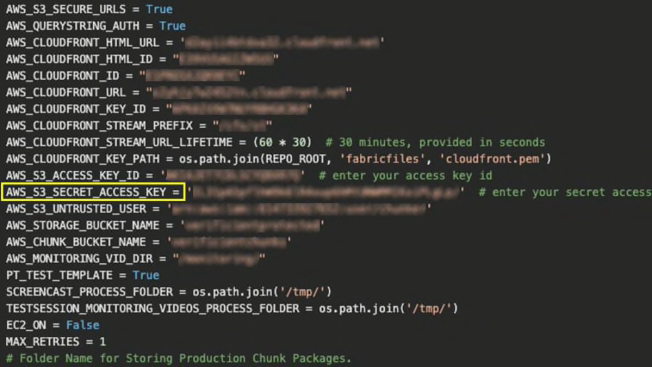
The code consisted of hundreds of files that appeared to run the Proctortrack service on the back end, connecting students to the company’s servers and databases. Satheesan and Johnson told CR that when they started digging through the code, they found problems far more serious than the company had let on, including what seemed to the students to be glaring security issues.
“We were deeply concerned by what we found,” CR’s Fitzgerald says. “The mistakes that were evident from even a quick look at the code looked like something that should never have gone into production.”
Jackson, the Disconnect CTO, agreed with the students’ and CR’s findings. (Disconnect has partnered with Consumer Reports on several investigations, along with the development of The Digital Standard, a framework to evaluate consumer technologies and how they respect consumer rights, including privacy and security.)
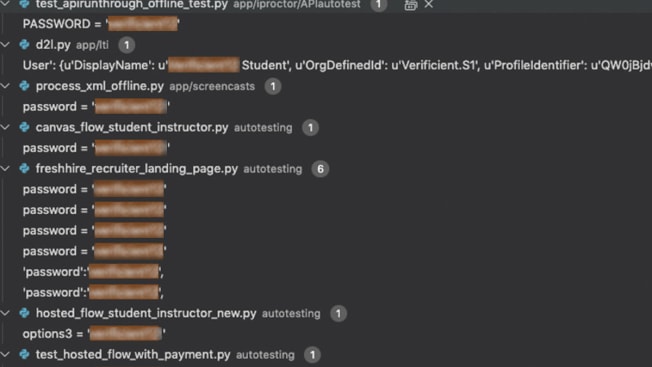
Most alarming, Jackson says, the source code contained what appeared to be many of the company’s own usernames and passwords. These included passwords labeled to suggest they’d unlock the databases for sensitive user information, company email accounts, and accounts for other companies and educational institutions. “It’s the keys to the kingdom,” he says.
The passwords appeared to grant any programmer working on the company’s software access to all the sensitive user data students uploaded to the service, from videos of their rooms to copies of their IDs, Jackson says. That’s a very poor privacy practice, according to him and other security experts: Typically, only a select number of employees can access personal data held by a company. The Proctortrack code also listed the same passwords reused for multiple accounts, and some were easy to guess—violating the password advice experts give to ordinary consumers.
na na
If that analysis is right, anyone who downloaded a copy of the source code once it was leaked online would have been able to access that data. Information such as names, ID card numbers, and educational details could be involved in identity theft or other crimes years from now, and no one would ever know that it stemmed from the data breach, Jackson says.
na na
This practice of “hard-coding” usernames and passwords by writing them into a computer program violates basic rules of digital security, Jackson says, because it makes it easy for bad actors to infiltrate computer systems. “It’s just pure laziness,” he says. “There are so many things that could go wrong.”
Kumar, the CEO of Proctortrack’s parent company Verificient, disputes Consumer Reports’ conclusions. He says that aside from a few insignificant exceptions, the passwords we saw were simply placeholders used during tests that were automatically replaced in the live version of the code, and that no user data was ever accessible by unauthorized employees or anyone else. “There are multiple barriers they need to cross before they can actually access our database and data,” Kumar says.
However, he agrees that some student email addresses were mishandled. “It was a mistake. Certainly, we should not have left it as part of the code base.” Kumar says he contacted St. George’s University about the issue—the university did not respond to CR’s questions.
Kumar did not answer questions about how hackers accessed the company’s website and email accounts if the passwords were just placeholders.
Jackson says the information in the Proctortrack code had the hallmarks of real login credentials, not placeholders, and there was no process in the code he examined for overwriting them all. Other elements of the programming were equally sloppy, Jackson concluded. He says, “All we can go off of is what the code says. They were clearly doing things they shouldn’t have been doing” to protect students.
Do you have information on privacy and security practices at online proctoring services that we should know about? We'd love to hear from you. Contact our reporter Thomas Germain at thomas.germain@consumer.org.
Sarah Zatko, a security expert and chief scientist at the Cyber Independent Testing Lab, reviewed Jackson’s findings and agrees with them. “It just smacks of something that was slapped together without a lot of concern for security,” Zatko says. (CITL has also contributed to the Digital Standard and has worked with CR on other projects.) And, she says, there’s little evidence to support Kumar’s claim that this code didn’t represent the way the system operated before the breach, or even that the problems have all been fixed now. “They haven’t given anything technical that could be verified by an outside party, and I find that highly suspicious,” she says.
Consumer Reports did not attempt to use any of the passwords in the code, which would likely have been illegal as well as unethical, because it could have accessed students’ data without their permission. Kumar invited Consumer Reports to review Proctortrack’s current source code and what he said was an independent security audit by an outside company, but only if CR agreed to sign a nondisclosure agreement preventing us from reporting what we learned. CR declined this offer. Jackson says that a review of the current state of the code would say little about any problems that existed before the breach.
It 'Makes Me Question the Value of My Education'
Many students who take issue with online proctoring services blame their colleges and universities. “You’re paying so much to be at school and to be protected, and you’re forced to use a program that you don’t even feel safe with," says Nguyen, the Western University freshman.
Consumer Reports reached out to a number of colleges that have used Proctortrack—Georgia Tech, Rutgers, Purdue, St. George’s University, MIT, Ohio University, and Western University—to ask how they had vetted Proctortrack’s privacy and security practices when they contracted with the company, and how they responded to the data breach.
Purdue, St. George’s University, and Western University did not respond to CR’s questions. Rutgers representatives say the university switched to another proctoring service, Respondus Monitor, in response to the breach. Georgia Tech told us the college primarily uses a service called Honorlock, though a few courses employ Proctortrack. MIT said the school hasn’t used Proctortrack since last summer and does not plan to use it in the near future.
Most schools didn’t provide information on how they ensure that the software they require students to use is safe. However, Georgia Tech says the school typically asks technology vendors to supply independent security audits. If one isn’t available, the school asks companies to describe their security practices in a standard auditing form called a HECVAT. Ohio University says software is reviewed by a multi-departmental committee to check for compatibility, compliance, accessibility, and alignment with IT best practices and standards.
In many cases, experts say, educational software does have security problems.
CR’s Fitzgerald spent years working with school districts and technology vendors to evaluate the privacy and security risks of educational software before joining CR. “These types of problems are all too common in software that’s used to surveil students. Development gets rushed, security gets short-changed, and schools often don’t have the staff, the resources, or the will to vet vendors," he says. "There’s no watchdog holding these companies accountable.”

Erik Johnson Erik Johnson
State and federal regulations require that “reasonable security measures” are in place to protect student data, says Girard Kelly, director of the privacy program at the nonprofit Common Sense Media. “Hard-coding credentials is not an industry standard practice,” he says. Schools have to make sure technology vendors are following the law through measures such as reviewing privacy policies and practices, and contractually requiring companies to protect student data.
However, investigations and lawsuits from state and federal regulators over security violations are rare, and most privacy laws don't allow students to sue companies for violating the rules, Kelly says.
“There aren’t enough reasons to care or chances of getting caught for most companies to put even the most rudimentary protections in place,” says Justin Brookman, the director of consumer privacy and technology policy at Consumer Reports. “That’s not going to change until more states or the federal government put robust security regulations in place.”
CR asked several leading proctoring services about their security practices but got limited responses. Jarrod Morgan, founder and chief strategy officer of ProctorU, which suffered its own data breach earlier this year, tells CR that the company “engages regular, outside, independent audits of its data policies and systems” but declined to discuss them publicly.
Proctorio CEO Mike Olsen says his company can provide the results of a security audit to schools but that they don't all have the sophistication to evaluate the reports. “We have some that don’t even know what they’re looking at when we send them that report.” (You can view a Proctorio security report, though it’s short on details.)
Proctorio has experienced its own controversies, such as public battles with critics including Erik Johnson—one of the students who contacted Consumer Reports—over a series of negative tweets in which Johnson discussed a Proctorio browser extension. Olsen says the tweets violated Proctorio copyrights, a claim Johnson disputes. The company has also sued a learning technology specialist for his tweets about Proctorio’s software.
All the problems he's seen with online proctoring services “makes me question the quality of my education, because of the fact that it takes a student to uncover something that should have been uncovered by the administration’s vetting process,” Johnson says.
Students Are Demanding Change
Tens of thousands of students have signed petitions calling on universities to stop using proctoring software. They include students at schools that have employed Proctortrack, such as MIT and Western University. “We reject this gross invasion of our privacy, and demand that alternative arrangements be made across the University,” reads a petition with more than 5,000 signatures from California State University Fullerton.
Kumar, CEO of Proctortrack’s parent company Verificient, says students have “valid concerns” and that he sympathizes with their discomfort. Proctoring software is “intrusive by nature” he says, but “if there’s no proctoring solution, institutions will have to totally change how they provide exams. Often you can’t do that given the time and limitations we have.”
C. Edward Watson, associate vice president for quality, pedagogy, and LEAP Initiatives for the Association of American Colleges and Universities, which has more than 1,000 member institutions, recommends against the widespread use of these services.
“When possible, educators should avoid using proctoring software altogether because the risk of exacerbating inequities between students is significant," Watson says. If the faculty members decide to use the services, he says, they should first study the risks and ramifications, and work with students to make the testing "as equitable as possible," he says.
The best option may be to find a different kind of test altogether, Watson says. “We should aspire to assess students in ways that have them apply knowledge, rather than engage in rote memorization and recall,” where cheating is more likely.
Some students see it the same way.
Quoting her own school’s policies, Lucy Satheesan, one of the students who contacted Consumer Reports, points out that Miami University tells its community, “academic integrity is about learning, responsibility, accountability, fairness, respect, honesty, and trust.” Satheesan says she and her peers just want universities to extend that respect and trust to their students.
Update: This article was updated to use Lucy Satheesan’s current name. The original version of the story used her previous name.
Correction: An earlier version of this article said that Proctorio had sued a security researcher. The lawsuit was directed against a learning technology specialist at the University of British Columbia.